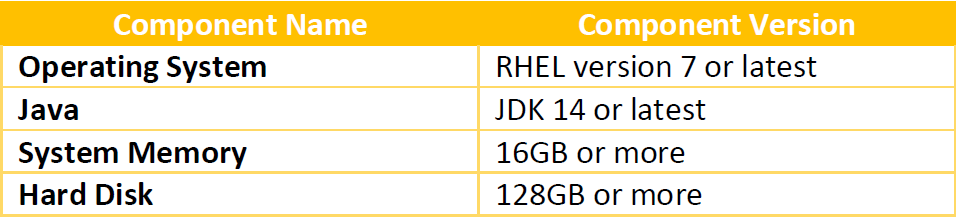
System Requirements #
Approach #
- User/Admin has bought a valid SSL certificate from the trusted vendors of Salesforce.
– Outbound Messaging SSL CA Certificates - User/Admin has got the deployment package and transferred it to the deployment server.
- User/Admin has exported the deployment package to the following directory.
/opt/skyvva-agent
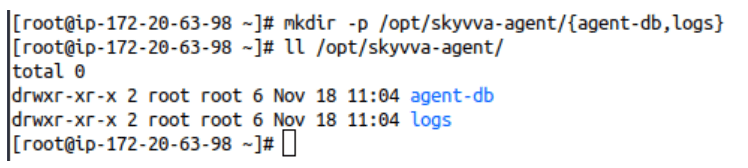
If the above directory doesn’t exist already then create it using the following command.
mkdir –p /opt/skyvva-agent/{agent-db,logs}
- Extract the deployment package using the following command.
tar –xvzf Skyvva-Agent-Deployment-Package.tgz -C /opt/skyvva-agent/
Deployment Procedure #
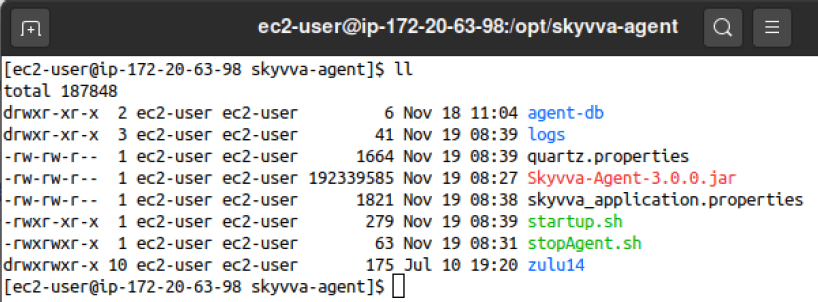
1. Once we extract the deployment package to the above-mentioned directory, we should be able to find the following artifacts in the above directory.
- Skyvva-Agent-3.0.0.jar
- quartz.properties
- skyvva_application.properties
- startup.sh
- stop-agent.sh
- zulu14
2. Now once we have all the artifacts available and extracted in the deployment directory, we can update the configuration in the skyvva_application.properties file.
• server.port=9055
The above property will set the port on which the Skyvva Agent will listen.
• skyvva.h2.db.port=9056
The above property will set the port on which the Skyvva Agent Internal database web console
will be available.
• skyvva.agent.username=skyvva
• skyvva.agent.password=skyvva@12!
3. After completing all the above steps, we can safely start the agent by executing the startup script.
• start-agent.sh
SSL Setup Procedure #
There are two parts to setting up SSL.
- The first part is where we enable SSL for the Agent instances so that all the services/endpoints exposed by SKYVVA Agent middleware can be access using SSL over http i.e. https protocol.
- In the second part, we need to ensure that SKYVVA Agent middleware can access the Salesforce org using https. In order to do that we will have to trust the Salesforce SSL certificate by adding the Root CA certificate of Salesforce org to Agent’s trusted keystore.
Setup SSL for Agent Instance #
2. Once we have copied the new SSL certificate to the deployment directory, we need to change the property file so that the Agent Instance can pick up the SSL certificate. Open the property file with the name skyvva_application.properties and look for the properties mentioned below.
[aux_code language=”javascript” theme=”tomorrow” title=”” extra_classes=””]# ==================================
# Agent SSL Properties
# ==================================
# Change this to true, if SSL has to be enabled
skyvva.h2.db.ssl.enabled=false
# Uncomment the following properties to enable SSL for Agent Services
#server.ssl.key-store-type=PKCS12
#server.ssl.key-store=/opt/skyvva-agent/ssl-certificate.p12
#server.ssl.key-store-password=Skyvva@12!
#server.ssl.key-alias=1
#security.require-ssl=true[/aux_code]
3. As we can see above, all the properties except one have been commented out (which means starts with ‘#’). We will have to uncomment them i.e. remove ‘#’ from the starting of the lines. Once done it will look like as shown below.
[aux_code language=”javascript” theme=”tomorrow” title=”” extra_classes=””]# ==================================
# Agent SSL Properties
# ==================================
# Change this to true, if SSL has to be enabled
skyvva.h2.db.ssl.enabled=false
# Uncomment the following properties to enable SSL for Agent Services
server.ssl.key-store-type=PKCS12
server.ssl.key-store=/opt/skyvva-agent/ssl-certificate.p12
server.ssl.key-store-password=Skyvva@12!
server.ssl.key-alias=1
security.require-ssl=true
[/aux_code]
4. Now we will have to change only 4 properties to enable the SSL for SKYVVA Agent. Those 4 properties are as follows.
[aux_code language=”javascript” theme=”tomorrow” title=”” extra_classes=””]skyvva.h2.db.ssl.enabled=true
server.ssl.key-store=/opt/skyvva-agent/Add the name of the new SSL certificate file
server.ssl.key-store-password=SSL certificate store password
server.ssl.key-alias=Alias of the SSL certificate
[/aux_code]
Once we have replaced the highlighted values with the right possible values, we can restart the Agent Instance.
Setup SSL for Outbound Flow #
In this section, we will see how to trust a Root CA certificate so that we can connect to any system like Salesforce, Kafka, SAP, etc using SSL through SKYVVA Agent middleware.
Normally all the standard CA certificates are already present in the Trust Store file used by the JDK(which is embedded inside the Agent Deployable Package), but in rare scenarios where it’s not available, we can import it as a trusted certificate.
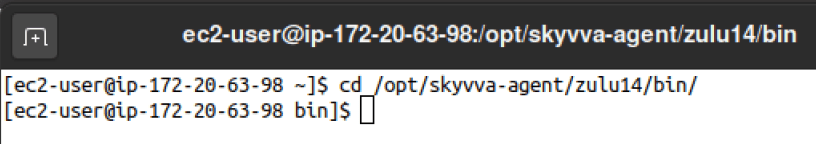
Procedure #
cd /opt/skyvva-agent/zulu14/bin
2. Use the command described below to import the certificate file as a trusted certificate.
[aux_code language=”javascript” theme=”tomorrow” title=”” extra_classes=””]keytool.exe -importcert -alias certificate-alias-name -file path_to_downloaded-certificate-der-file -keystore /opt/skyvva-agent/zulu14/lib/security/cacerts -storepass changeit -trustcacerts
[/aux_code]
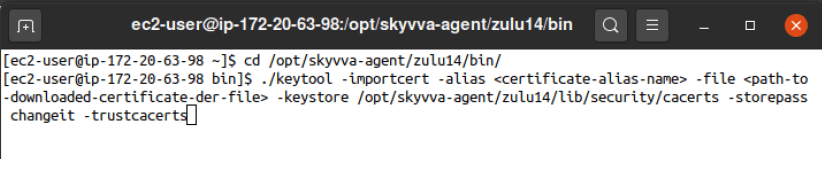
Make sure that you replace the highlighted parts with the actual values before executing the above command. Once done, restart the Agent Instance.
Procedure to Download on SSL certificate #
Google Chrome #
Export the SSL certificate of a website using Google Chrome:
1.Click the Secure button (a padlock) in an address bar.
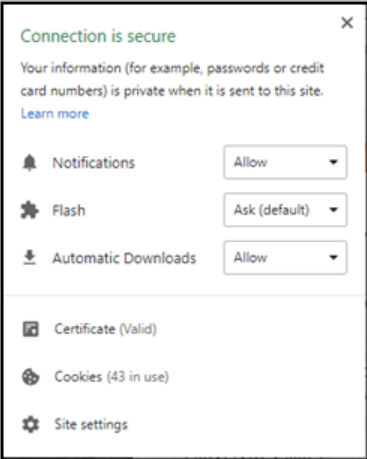
2. Click the Certificate(Valid).
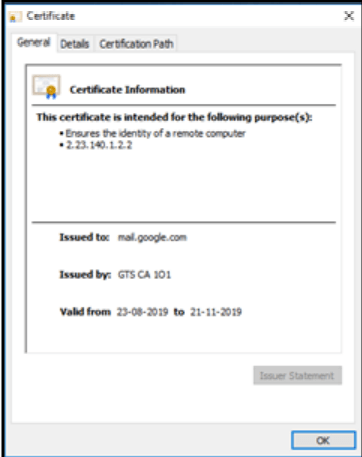
3. Go to the Details tab
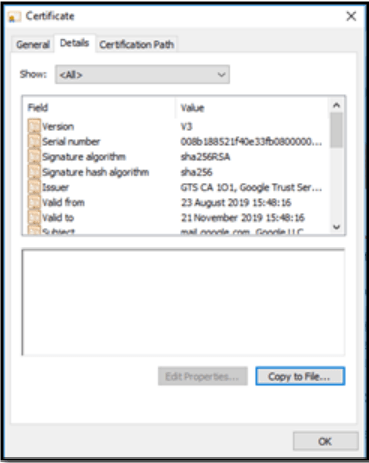
4.Click the Copy to File… button
5.Click the Next button.
6.Select the “Base-64 encoded X.509 (.CER)” format and click the Next button.
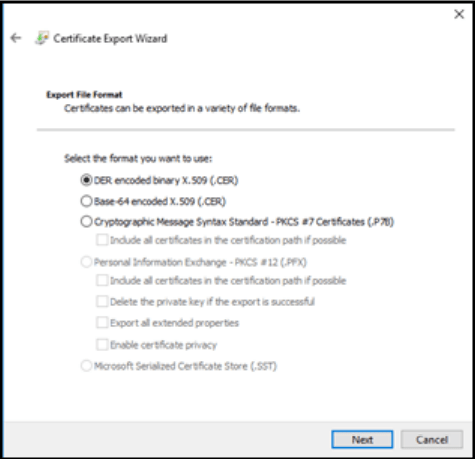
7.Specify the name of the file you want to save the SSL certificate to
8.Click the Next and the Finish button
Mozilla Firefox #
Export the SSL certificate of a website using Mozilla Firefox:
1.Click the Site Identity button (a padlock) in an address bar.
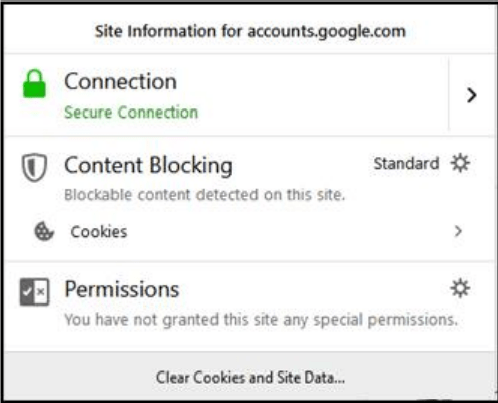
2.Click the Show connection details arrow
3.Click the More Information button
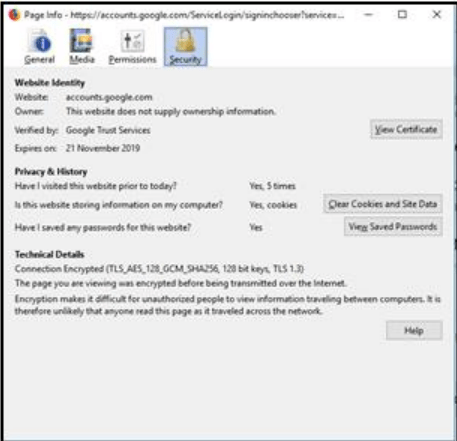
4.Click the View Certificate button
5.Go to the Details tab

6.Click the Export button
7.Specify the name of the file you want to save the SSL certificate to, keep the “X.509 Certificate (PEM)”
format and click the Save button
Internet Explorer #
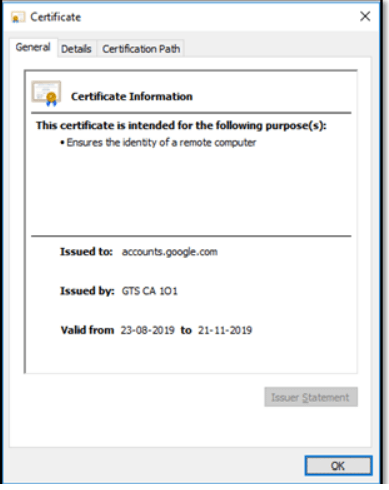
Download and save the SSL certificate of a website using Internet Explorer:
1.Click the Security report button (a padlock) in an address bar
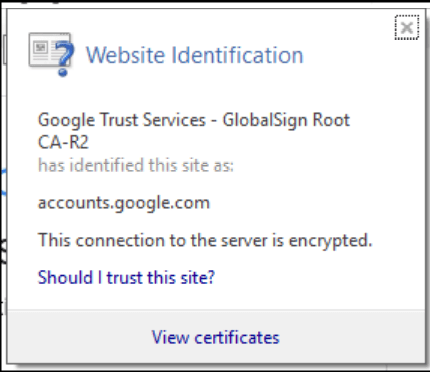
2.Click the View Certificate button
3.Go to the Details tab
4.Click the Copy to File… button
5.Click the Next button
6.Select the “Base-64 encoded X.509 (.CER)” format and click the Next button
7.Specify the name of the file you want to save the SSL certificate to
8.Click the Next and the Finish buttons



